
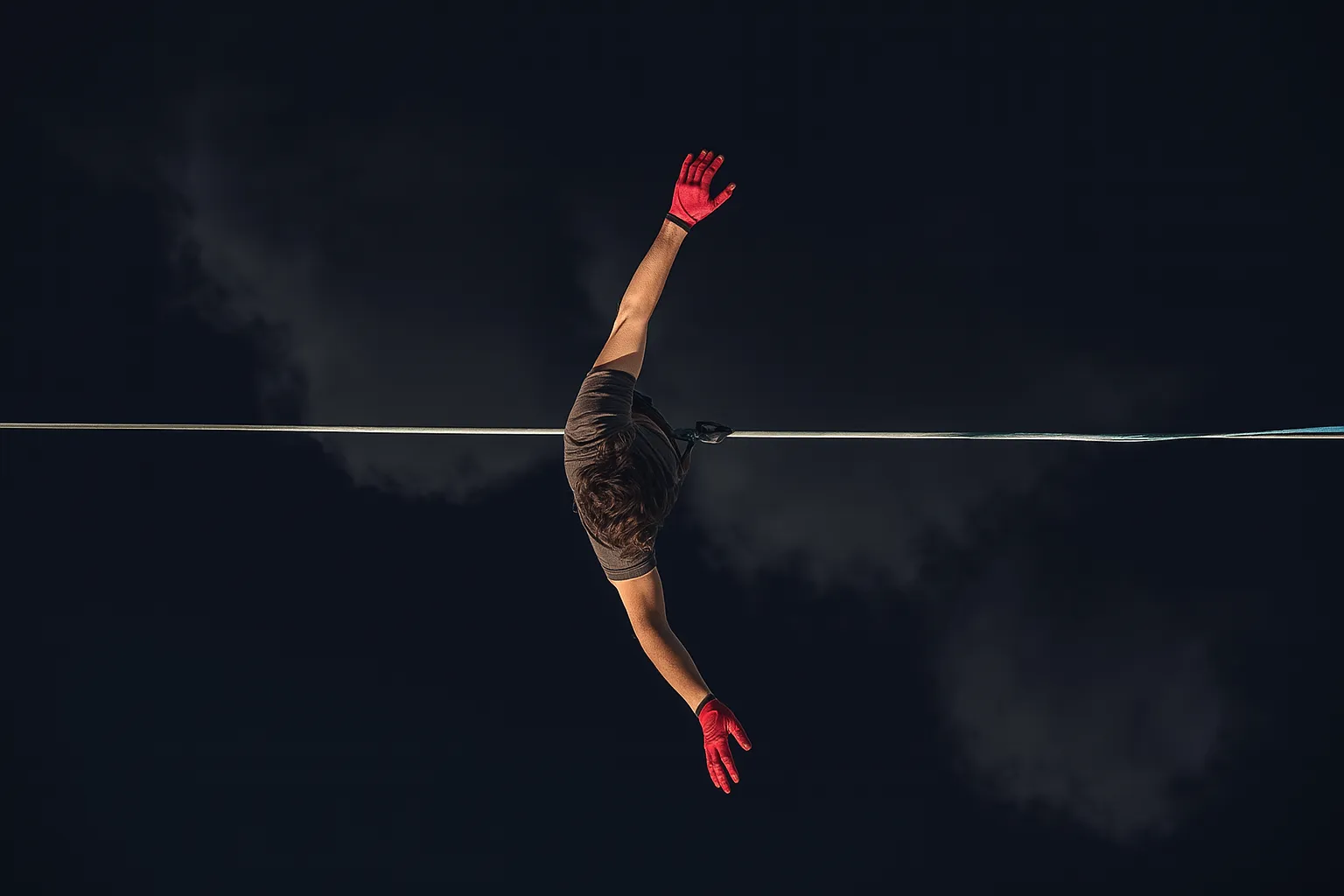
There is a precise moment in every developer's career in which the security of the code that runs on their machine clashes with the unpredictability of production.
It's that moment when you realize that there is a difference between "hello world" and "system that supports millions of users". an abyss made of architecture and infrastructures that have a life of their own, and technical decisions that are transformed into concrete economic consequences.
In the world of containers and microservices, this moment comes faster than you imagine.
Kubernetes is a living ecosystem, to be explored and fully understood: made up of unwritten rules, recurring behaviors and lurking traps that await even the most prepared.
Anyone who believes they can master it with a few tutorials and a lot of good will will discover the difference between who survives and who is overwhelmed by its complexity: it does not lie in the skills, but in the mentality with which it faces change.
Here it is not enough to accumulate technical skills, those can be acquired through study and practice.
The real difference lies in developing what I call "architectural instinct", that is, the ability to perceive a risk before it manifests itself.
An imminent risk, hidden between the lines of code or in the silence of an alert that doesn't sound.
The sensitivity of feeling when a system is about to break, before it even happens.
To understand the weight that every technical choice brings with it.
And, above all, to recognize recurring failure patterns before they turn into operational disasters.
This is not a theoretical manual on containers.
It is the map of a real territory that I crossed, learning everything I could.
It is the price you pay in sleepless nights that never end, in choices that take your breath away, in the daily weight of choices that seem right but instead open up new cracks.
But it is also the story of a transformation: one that starts from the fear of the unknown and reaches full mastery.
A mastery that doesn't ask you to become cold or distant in the process, but to stay human.
Because behind every software architecture there is always, inevitably, a human story.
What is Azure Kubernetes Service and why 73% of developers fail on their first deployment

Have you ever felt that pang in your stomach when you're about to deploy an application and you don't know if it will hold up to the first spike in traffic?
That moment when you realize everything you've learned on tutorials It didn't prepare you to the complexity of the real world, where every wrong configuration is a concrete danger.
A danger of downtime, crazy cloud bills and endless hours trying to understand what went wrong: this is the feeling that 73% of developers who approach AKS know well.
The illusion of simplicity crashes into reality of container management, AKS is not simply a service to manage them; it is a complex and delicate ecosystem.
An ecosystem that orchestrates thousands of interconnected components, each with its own rules, dependencies and potential breaking points that can suddenly explode.
When Microsoft presents AKS as "managed Kubernetes", it leaves out a crucial detail: managed does not mean simple, and simple doesn't mean you can ignore how it works.
The result?
Deployments that seem to work in development but fall apart in production, configurations that become a nightmare, costs that grow without apparent explanation.
Costs that rise out of control because no one has ever explained it to you every allocated resource has a price and every architectural decision has real long-term consequences.
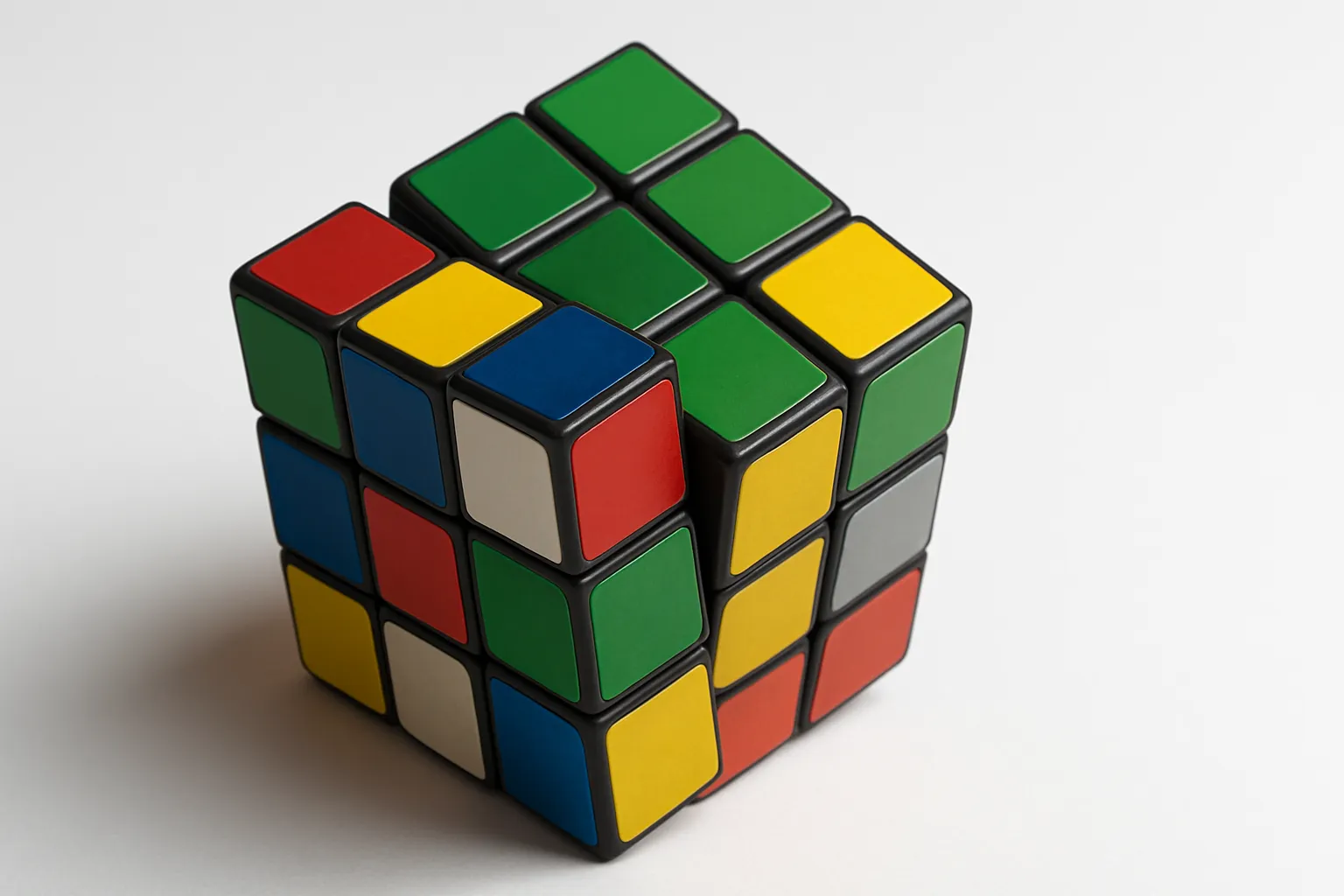
The difference between those who dominate AKS and those who are dominated by it lies in the understanding of a fundamental truth: Kubernetes is not just a tool, it is a language that you must learn to think.
Like any language, it has a grammar, a syntax and an internal logic that you have to internalize before you even start writing, otherwise chaos is inevitable.
You can copy YAML manifests from the Internet, follow step-by-step tutorials, and even complete certifications without really understanding what's happening in your cluster.
But if you don't understand why a pod is scheduled on one node rather than another, why a service can't reach its endpoints, or why your cluster consumes too much; then you're sailing blind.
You're just postponing the moment when reality will present you with the bill with very high interest, and it will be too late to improvise.
But it's not too late to change your perspective and transform that fear into controlled mastery.
Create an AKS cluster without falling into the 5 traps that cost thousands of euros
There is a fine line between elation and naivety when, for the first time, a customer builds their own AKS cluster and proudly watches the rapid activation of each service.
It is at that moment that the illusion is born: the sensation that everything is finally under control, that all you have to do is press a few buttons to get the scalability promised by the cloud.
But the reality reveals itself a few days later, with the punctuality of a bank account that begins to empty.
Those resources that are so easy to activate come with a price that no one had dared to mention.
Each click is transformed into a cost item, discreet but relentless, which it can grow to become unsustainable without even realizing it.
What seemed like a few dollars a day can turn into hundreds of dollars a month, driven by the default sizes offered by Azure, designed for enterprise scenarios with six-figure budgets, not for projects that have yet to prove their value.
Here is the first trap: choosing a "standard" virtual machine, apparently harmless, and instead finding yourself incurring a fixed cost multiplied for each node, which in a cluster always starts with at least three machines.
In an instant the annual total exceeds two thousand euros, before having even published a single line of code in production.
The second trap is more subtle, like a deception disguised as a life-saving feature.
Autoscaling, if configured poorly, it can become an uncontrollable monster: you activate the autoscaler cluster convinced that it will optimize everything for you, and instead you discover that during a traffic peak the nodes multiply irrationally and remain active, unable to shut down because some background process keeps them busy indefinitely.
There was a case, during a practical session of Azure course, which deserves to be told as a perfect technical mystery.
One participant had created a seemingly flawless setup: high availability, autoscaling, full monitoring.
Yet, behind that apparent perfection, there was a monthly bill of three thousand euros, for an application that generated ten times less in revenue.
Every component had been beefed up to the max: high-end storage, redundant load balancers, a cluster distributed across multiple geographies.
No one had thought that those options, added together, would multiply the costs to the point of making them unsustainable.
The real lesson?
Start with the minimal configuration, as essential as possible, without being seduced by hypothetical scenarios that do not yet exist.
Organic growth, driven by data and not by fears, allows you to scale only when really needed, safeguarding the budget and sustainability of the project.
Choose simple resources, less expensive machines, standard storage, and set conservative autoscaling limits.
You can always raise them later, when your real traffic grows and you are sure you can afford it.
Don't make the mistake of designing an infrastructure for all the possibilities in the world when you haven't validated your idea yet.
The true cost of AKS, like any well-crafted mystery, is not what appears on the first invoice: it is the price you pay when you realize having built a castle that was too expensive to stay standing for a long time.
If you really mean to govern a cluster instead of suffering it, prove it now: tell us how you would approach your next high availability scenario.
I bet you might be surprised by how much more you can learn.
Deploying containerized applications: Why 90% of tutorials lie to you

There is an almost visceral frustration that grips those who, full of enthusiasm, follow an impeccable tutorial, only to discover that in their real environment everything breaks spectacularly.
It's a feeling of loss, like finding yourself in a dark villa after the tour guide had only shown you the lit rooms.
The customer in question had followed every instruction to the letter, believing that a successful deployment in someone else's lab could ensure identical success in their cluster.
But behind the brilliant demonstration there was a deception: incomplete configurations, privileges that were too high, resources that did not exist in reality, a house of cards ready to collapse.
At that moment he realized that the demo had been set up like a theatrical script, with perfectly set up wings and no space for improvisation.
Network rules they were custom built, integrations set up in advance, and security checks virtually ignored.
All perfect for a show of a few minutes, but dangerously fragile in production.
It's like learning to drive a sports car on a private circuit and then finding yourself in city traffic, between potholes and chaotic intersections, with the same car at full speed.
The truth no one tells is that deployment is just the beginning of the mystery, not the solution.
Bringing a service from the "created" state to the "active" state does not mean having solved it, but only having moved the complexity on your shoulders: communications between distributed components, intelligent health checks, management of processes that can die and be reborn without warning.
And it doesn't end here.
You have to master changing memory limits, unpredictable workloads, storage that fills up at the worst time.
And just when you think you have everything under control, monitoring comes: logs that get lost, processes that vanish and reappear without leaving a trace, like suspects in a mystery novel.
The client understood that the real strategy does not start from success, but from failure analysis.
You don't design a robust infrastructure by thinking about what works, but by imagining everything that could go wrong: undownloadable images, external services crashing, nodes terminating unexpectedly, networks saturating, storage close to collapse.
Alone when you know how to anticipate disaster you can build something solid, which doesn't collapse at the first twist.
Because the difference between a showcase deployment and a production-ready one lies in the ability to manage the unexpected, not in replicating a textbook demo.
Anyone who thinks that a few lines of YAML is enough to tame the chaos of containers would do well to think again.
The real game only begins when the system rebels against your expectations, night after night, in an environment that never sleeps.
Manage the lifecycle of containers when everything seems to be on fire

There's a moment, usually at three in the morning during the first month in production, when you realize that launching a container is like adopting a pet.
It seems easy until you understand that requires constant care, continuous attention and the ability to interpret signals that are not always evident or immediately understandable.
You wake up with an alert indicating something serious, you open the control panel and find a desert full of components that continue to restart without success, while some services try in vain to reach destinations that no longer exist.
Then comes the terrible realization that any attempt to fix things could make an already critical and out-of-control situation worse if you don't act with clarity and method.
It's the moment you understand that the container lifecycle is not a linear sequence of events, but a dynamic ecosystem where every change generates ripple effects.
Effects that ripple through the entire system, often without warning, and the problem is that Kubernetes treats your containers like livestock, not pets.
But you still think of them as physical servers with persistent names, personalities, and states, and every time a pod is terminated and recreated it feels like a small failure.
It is not "fixed": it is a completely new entity that inherits configuration and responsibilities from its predecessor, but not its history, logs, or active network connections.
This paradigm shift is devastating for those coming from the world of virtual machines, where a reboot is an exceptional event often fixes known problems.
In a managed environment, a reboot is not an exception: it is the norm.
But if you're not ready, every restart can trigger new problems.
Managing the life cycle means accepting that destruction is an integral part of functioning.
It means accepting that your processes will continually be born, die, and reborn, and that your application must not just survive, but perform at its best in this ecosystem of controlled instability.
In Azure course I dedicate an entire module to this aspect because this is where amateurs separate from professionals, those who launch from those who design.
Anyone can launch a container, but manage its evolution over time it requires a completely different mindset, shaped by experience and continuous observation.
To address this challenge, there are some rules of thumb that every professional should integrate into their way of designing and deploying applications in an orchestrated environment, including:
- You have to learn to think in terms of rolling updates that keep the service running while gradually replacing instances without causing noticeable disruption.
- You need to think more carefully about the signals the application sends when it starts up or has problems, so as not to risk shutting down instances that are working properly.
- You need to ensure that when an instance is shut down, it can complete ongoing operations first, so as to avoid sudden crashes or data loss.
- You should be aware that any update may have to be canceled at any time; therefore, your strategy must always allow you to go back safely and without inconsistencies.
Lifecycle mastery manifests itself in the ability to orchestrate complex changes without downtime and diagnose problems by observing patterns and signals.
Not isolated symptoms, but recurrent behaviors, and above all design systems that improve automatically over time instead of degrading as releases go by.
When you reach this level, you're no longer managing containers: you're directing a symphony of software components that autonomously adapt, evolve, and self-heal.
However, even the best lifecycle orchestration collapses if you don't have visibility into what's really happening in your distributed ecosystem.
Anyone who doesn't approach the life cycle of containers with the right clarity ends up overwhelmed at the first mistake.
Enter your contacts: we will set up a dedicated time together to verify the solidity of your approach.
Security and permissions in Azure Kubernetes: when you discover that "it works" it doesn't mean "it's safe"

Have you ever felt that chilling sensation run down your spine when you realize that your "fully functioning" cluster is actually a playground open to all?
That moment when you realize that the application you have successfully deployed has unrestricted access to the entire system, and that confidential information is visible from any running component.
And that you've essentially built a supercar without brakes or seat belts, is the feeling every developer feels when they discover the brutality of the defaults in Kubernetes.
Because in Kubernetes, by default, everything is allowed until you explicitly say no, and the difference between "accessible" and "exposed" is as thin as the line between genius and madness.
Security in Azure Kubernetes Service it is not an external addition to your architecture, it is the DNA that must permeate every decision from the first moment.
When you assign global privileges "just to make everything work", you're not solving a technical problem: you're building a backdoor.
A silent access route, ready to be exploited at the worst moment.
And when you configure a component with no resource limits or minimal security measures, you're not making it easier: you're opening the door wide to anyone who wants to consume the entire cluster or snoop around the host's filesystem.
It's not practicality.
It's pure exposition.
It's like building a house where every window is always open and every door has no lock, justifying it with "it's more convenient to go in and out" at any time.
The problem is that Kubernetes security is so granular and complex that many teams treat it as a future issue to be addressed only in production advanced.
Security is not added later with a few more rules: it is planned from the beginning.
Every decision about facilities, access and visibility determines the risk you are accepting, whether knowingly or not.
In Azure course we tackle this topic from day one because I learned the hard way that it is infinitely easier to design security than to adapt it to an already existing system.
The strategy that works is that of the "principle of least privilege applied with constructive paranoia", each component should have only the strictly necessary permissions.
This means assigning only the strictly necessary permissions to each part of the system, avoiding unnecessary or too broad access.
It means preventing dangerous configurations at the root and manage access to resources securely, without leaving visible credentials in the code.
Perfect security doesn't exist, but an architecture designed to contain damage can transform an attack into a manageable incident, rather than a crisis that overwhelms the entire company.
But even the most rigorous security collapses if you don't know how to translate theory and best practices into systems that actually work under pressure, in real, unstable environments.
Monitor and scale AKS: How to stop discovering problems from customers

Have you ever received that laconic message from a customer: “The service is not working”, while your dashboard, placid as an irreproachable butler, continues to show you only green lights?
It's a moment of pure bewilderment.
You realize that your monitoring tools are lying to you and that, behind the reassuring facade, the system has already fallen apart.
It is precisely there that the subtle and crucial difference between monitoring and observability arises.
Monitoring tells you that everything seems fine.
Observability, on the other hand, reveals the truth to you, even when it hurts: like those requests that fail because a service takes 31 seconds to respond, while the gateway only allows 30.
Traditional monitoring was designed for orderly, predictable, stable worlds.
But Kubernetes, with its mobile and changing nature, redefines the rules every minute.
Here, components change identity, location, and state with the speed of an illusionist, and knowing that a node consumes 40% of the CPU may mean absolutely nothing.
You might watch a seemingly healthy app while ten containers compete for the same resources in a silent war that undermines performance without raising a single alarm.
Looking at average latency, for example, can be an elegant deception: those 200 milliseconds don't tell you that 5% of users are waiting 20 seconds for a simple click.
It's like checking the average temperature of a hospital and concluding that everything is fine, without realizing that the ICU is already burning.
True observability in AKS requires a multi-dimensional vision.
It is necessary to combine quantitative metrics, detailed logs and tracing capable of reconstructing hidden links.
Only in this way can you draw the complete map of the system in your mind, recognizing the first signs of drift well before they turn into a catastrophe.
An unusually long startup time for pods, an anomalous distribution of requests, or a new link between memory and latency are all signs worth their weight in gold.
It is these details that a truly intelligent alert must focus on, not the simple symptoms on the surface.
In this framework, automatic scaling is not a trivial mechanism, but a balancing act.
Set usage thresholds for adding resources, betting that new pods will be ready before traffic overwhelms existing ones.
And like any bet, if you lose it, the price is paid dearly: users experience slowdowns right at the most delicate moment.
The winning strategy is predictive.
Analyze historical patterns, leverage machine learning algorithms, learn the demand cycles of your business.
Only in this way can you climb before problems become apparent, transforming resilience into a competitive advantage.
To do this in a systematic and replicable way, you can focus on some basic operational practices like these:
- Analyze resource usage trends over time to understand real peaks.
- Check pod startup times under high traffic conditions.
- Simulate anomalous loads to identify latent failure patterns.
- Cross-reference performance metrics with business data to anticipate demand.
Eventually, when you truly master monitoring and scaling, you understand that the challenge is not to make a single service work, but to orchestrate a multitude of microservices that work together without destroying each other.
This is the difference between an illusion and a system that holds up, even under the most merciless light.
Best practices for microservices: beyond tech conference propaganda
Have you ever attended a conference where some tech lead of a FAANG company explains to you how microservices have revolutionized their architecture with extraordinary results?
From monthly deployments to hundreds of deployments per day, from teams blocking each other to autonomous squads innovating at the speed of light, it all seems perfect.
And have you ever tried that feeling of inadequacy when do you realize that in your real environment, after six months of migration, you have more problems than before and more complex deployments?
You've discovered that distributing your application across twenty different services also means distributing problems across twenty attack surfaces to monitor and manage.
Microservices propaganda hides the reality: They work beautifully when you have teams with decades of experience in distributed systems and budget for tooling.
And especially when your organization is already structured to manage the complexity that comes from decomposing a monolithic system into dozens of interconnected services.
In the real world, many companies adopt microservices for the wrong reasons: technology hype, management pressure, or simple imitation of what others do.
They do it with the wrong skills: developers accustomed to thinking in terms of centralized applications, and with organizational problems never really solved.
The problems that made their original monolith complex remain, but they become more fragmented and difficult to manage when each part of the system is separated.
The result is what Martin Fowler calls a "distributed monolith": all the complexity of distributed systems, but none of the benefits of modular architecture.
It's what we call 'architectural pragmatism' in Azure course: it's not about blindly applying patterns, but understanding when and how to break them to get results.
Microservices are not a goal, they are a consequence: if your organization does not know how to develop and deploy components independently, it will make them a problem.
Decompose the application into separate services it won't solve anything, it will multiply it, the right question is not “how do we migrate to microservices?” but "what's stopping us?".
What are our organizational and technological bottlenecks, and how can we solve them incrementally and measurably without chasing architectural fads?
The strategy that really works is the data-driven one: we start by identifying the natural separation points, where the links between components are weak and the responsibilities are well defined.
Extract the first service only when you have demonstrated the ability to manage distributed deployment, monitoring and debugging, and measure each step to verify the real benefits.
Every microservice it should solve a concrete problem of scalability, performance or team autonomy, don't just be a piece of code with a REST API in front of it.
And when you finally manage to make the microservices architecture really work, you realize that the real problem was never in the app but in the integration with the ecosystem.
With your organization's technology ecosystem, that's why the next step is the most critical and underrated: integrating with the Azure ecosystem.
Microservices reward only those who dare to question every certainty.
Leave your details now and prepare to be contacted for a personal evaluation of your architectural choices.
AKS integration with Azure: the myth of simplicity that no one dares to dispel

“It integrates seamlessly with all Azure services.”
It's a promise that sounds reassuring, almost hypnotic.
Yet, for many, it turns out to be the most wasteful lie that cloud computing has ever whispered.
A promise as seductive as it is deceptive, capable of making people believe that connecting AKS with the database, archiving, user management and monitoring is just a matter of a few clicks.
But every integration adds a new layer of complexity, like dominoes ready to fall.
Those complexities can turn a seemingly stable configuration into a maze of fragile dependencies, difficult for even experienced teams to crack.
It's as if they told you that you can connect all the appliances in the house to a single socket, just because they "use the same electricity", forgetting to explain the risks of overload capable of short-circuiting everything.
The first shock comes when you discover that “native integration” does not mean “automatic configuration”.
You find yourself immersed in hidden details, with a web of permissions, roles and identities that require surgical precision to avoid becoming a boomerang.
Connecting AKS to your access management system isn't just about enabling SSO; it means building a solid chain of trust between applications, managed identities and roles, both on the Azure and Kubernetes side.
A single mistake in this chain can shut down the entire system: developers unable to log in, pods unable to reach resources, error messages so vague they seem like clues left by a fleeing killer.
It's the frustration of know that it should work, without any tools to understand where to intervene.
The truth is that each Azure service brings with it its own security, network and operational logic model, often unwilling to collaborate with others.
And this silent conflict remains invisible until you are forced to bring it out.
When you connect AKS to your database, you can't ignore connection reuse management, failover mechanisms, or the risk that containers will keep open connections even after they've been closed, eating away at valuable resources.
If you don't set clear boundaries, you'll end up with a database saturated with orphaned connections that choke the entire system.
With Azure Storage, the issue is no less thorny.
You must be able to distinguish between files, objects and disks, choose appropriate performance levels and protect credentials carefully, never leaving them embedded in the code as compromising evidence.
The most solid strategy is not instant integration, but a gradual and controlled path.
Start from the simplest and most indispensable connections, such as identity and storage, then extend only after having validated every single step.
At each junction, implement detailed logs, test failure scenarios, build a plan B to survive the unexpected.
To give substance to this gradual approach, it is useful to follow some good operating practices such as these:
- Document every configuration from day one for clarity and traceability.
- Define simple, tested rollback procedures to reduce the risk of crashes.
- Set targeted alerts on permissions and privileged access, to anticipate any flaws.
- Keep your dependency inventory up to date, to avoid hidden breaking points.
A resilient architecture is recognized not only by what holds up 99% of the time, but by how it reacts to that single moment of failure, when every second is worth more than any SLA.
And before you even put all this into motion, remember one fact that too many only find out after the disaster has occurred: Security is not a luxury you can add later.
It is the first defense, the first truth, the only truly reliable shield in a world where every click can become a crack.
Practical example: from zero to production without making mistakes

There was a sense of security that November night, as if every cog had been oiled to perfection.
The client, a well-known brand in online commerce, was anxiously awaiting the arrival of Black Friday, convinced that the new cloud architecture would hold up without batting an eyelid.
The managers had guaranteed it: “scalable, resilient, infallible.”
And so it was, at least for a while.
The first few hours passed without a hitch, with sustainable traffic and orders flowing like a calm river.
But, as often happens on the longest nights, danger lurked in the shadows, ready to strike.
At 2:47 in the morning, just when the first eager buyers were waking up in the United States, the system revealed its true fragility.
It wasn't an obvious error, nor a scandalous bug that caused it to collapse, but a set of tiny cracks, imperceptible to a cursory glance, which together caused the collapse.
The first blow came from the heart of the database.
A seemingly sufficient setup in testing proved dramatically inadequate when hundreds of users began completing checkout at the same time.
Connections, like travelers stuck at a level crossing, they accumulated until every exit was saturated.
The response time, once as quick as a gunshot, turned into an exhausting thirty-second wait.
In a panic, someone decided to scale up the resources, but the procedure took fifteen interminable minutes, leaving the platform completely paralyzed, at the mercy of frustrated customers and failed orders.
The second shot was even subtler, like a knife blade in the fog.
Autoscaling had been confidently set up on the CPU, but no one had considered that the application was actually dependent on data access.
So the servers multiplied without any real effect, unable to overcome the database bottleneck.
It was a bitter night.
A night that taught that customer a merciless truth: the illusion of "a few clicks" and "cloud magic" is not enough to protect a business.
You need method, rigor and a production contract written with the precision of an investigator.
If only they had mapped out the most important paths for users, such as registration, login, search and payment, with precise parameters, everything would have been different.
That would have been enough set response thresholds, success rates and emergency strategies capable of containing the damage before it was too late.
Today, thanks to that lesson, there is a method that could be defined as mystery-proof: the three-ring methodology.
An approach that takes care of technical resilience (load balancing, health checks, automatic recovery), operational resilience (proactive monitoring, intelligent alarms, rapid intervention plans) and business resilience, with clear and honest communication towards customers in the darkest moments.
A plan that leaves nothing to chance, because even the smallest crack, if neglected, can become a disastrous collapse.
Just like in a well-orchestrated mystery, where every clue counts, and every forgotten detail can turn into the final twist.
In the Azure course we apply this framework step-by-step on real cases, because theory is measured at 3 am when everything goes wrong and quick decisions are needed.
When you master the three rings, you no longer manage emergencies: you prevent them before they happen, and when they happen, you transform them into system-strengthening opportunities.
But maybe, after reading all this, you're wondering if it's really worth dealing with so much complexity or if there's a way to skip sleepless nights and years of mistakes.
Now is the time to choose who you want to become.
Nobody tells you that when you start working with complex technologies like Azure Kubernetes Service: you're not just learning a tool, you are choosing who you want to become.
You can remain the one who copies configurations from the network, hoping they work, or you can become the one who understands the systems so deeply that you can bend them without breaking them.
The path is clear: you can continue to navigate by sight, learning from costly mistakes and emergency situations that put your professional reputation at risk every time.
Or you can choose to invest in deep understanding that transforms you from someone who "knows how to use Kubernetes" to someone who really knows how to manage complex systems.
I'm not selling you a course, I'm offering you a concrete and lasting transformation that can forever change the way you work, think and deal with problems.
The Azure course it's not a collection of tutorials or certifications to show off on LinkedIn, but the bridge between where you are today and where you could be in six months if you choose to cross it.
When colleagues and managers turn to you to solve impossible problems, when your deployments work first time even under pressure.
And best of all when you'll sleep soundly knowing that your systems are not just designed to survive, but to thrive in complex, dynamic environments.
The question isn't whether you need these skills, but why you already know the answer, the question is: how much longer are you willing to wait before actually taking action?
How much longer has to pass before you become the person you wanted by your side that night in 2019, when everything seemed to be on fire and you didn't know how to put out the fire?
Your professional future is waiting for you, with new challenges, new recognition, new possibilities, all you have to do is decide and go get it.
